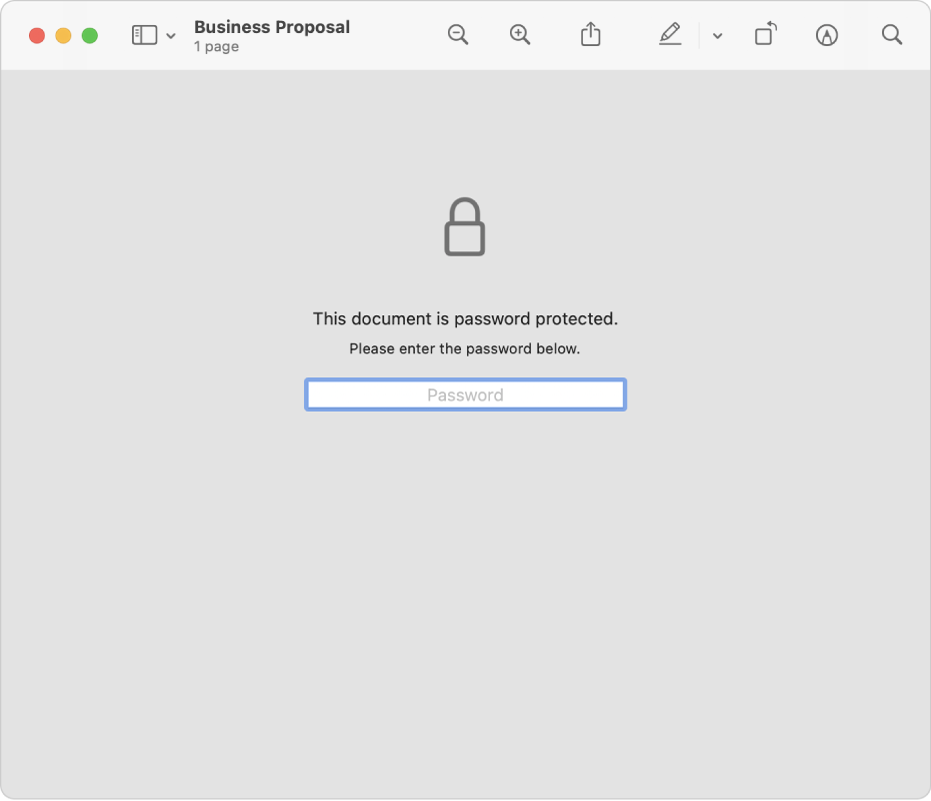
- Password Encryption
- Free File Encryption Software For Mac
- Online Password Encryption
- Best Free File Encryption Software For Mac
- Free Folder Encryption
Can you encrypt your computer so as to lock important files, folders, and even a whole hard drive partition? Yes. This page covers 5 best PC encryption software that you can flexibly free download and apply to protect your data or business secrets.
By following this page, both Windows and Mac users can find a file locking or folder encryption solution here. Let's start.
Encrypto is a free, easy-to-use app that lets you encrypt files with AES-256 encryption and then send them to friends or coworkers. It works on both Mac and Windows, so you can send encrypted files without worrying whether the other person can open it or not. Take any file or folder and add AES-256 encryption to it. Encrypt PC with EaseUS LockMyFile - Paid. Supported OS: Windows OS. Produced by: EaseUS.

What Is PC Encryption Software
To get started, let's first learn what is Encryption Software. Definition: Briefly, encryption software is a tool or program that uses the cryptography algorithm to prevent unauthorized access to digital data on a storage device, local disk on a computer or server machine, or a cloud-based drive.
Similarly, PC Encryption Software is software that uses encryption technology and cryptography algorithm to lock a file, a folder, and even a local or external hard drive. Currently, PC encryption software is widely used on both Windows and Mac computers.
If you are looking for reliable PC encryption software or you need a guide to encrypt or password-protect files, folders, local or external hard drives, luckily, this is what we are about to talk about next. Read on and find your answer below.
5 Best PC Encryption Software for Windows and Mac in 2021 | Free & Paid
Installing antivirus software on your PC doesn't mean that your files and data are 100% secure on your computer. Trojans, malware, and even hackers still can find accesses to your privacy and business secrets.
To keep your essential files securely protected, we collected 5 best PC encryption software in 2021 that are listed here below. You can simply select one and follow its respective guide to take care of your private information now.
| PC Encryption Software | Pros | Cons |
|---|---|---|
| EaseUS LockMyFile (Paid) |
|
|
| AxCrypt (Paid) |
|
|
| FolderLock (Paid) |
|
|
| BitLocker (Free) |
|
|
| VeraCrypt (Free) |
|
|
How Do I Encrypt My PC with Best PC Encryption Software? Your Reliable Guides Are Here
Here you'll see a respective tutorial guide on using different software to encrypt or lock computer files. Go and follow to start encrypting your PC data now:
#1. Encrypt PC with EaseUS LockMyFile - Paid
Supported OS: Windows OS
Produced by: EaseUS Software
Free Download: Click the button below to free download it.
EaseUS LockMyFile is a new life, folder, and drive locker application which enables all levels of Windows users to keep their files, folders safe. With it, you can flexibly encrypt a file, lock a folder, hide a partition, and protect files on a local computer drive. You can also apply it to encrypt or lock files on an external hard drive or even a network shared drive. So how to apply this tool to encrypt your computer disk? Let's start here.
How to Use:
Step 1. Enter 'easeus' to launch EaseUS LockMyFile, register with a valid email and a license code.
Step 2. Click File Encryption under More Tools > Click Add Files or Add Folders.
Step 3. Select important files or folders that you need to encrypt, and click Open.
Step 4. Select the encryption mode: Encrypt to gfl or Encrypt to exe.
Step 5. Browse a safe location on your PC, rename the encrypted file or folder, and click Save to save the encrypted files/folders.
Now, your drive is safely locked and encrypted. No one can access your drive. To encrypt more drives on your PC, repeat the above steps.
#2. Encrypt Computer with AxCrypt - Paid
Supported OS: Windows OS, macOS.
Password Encryption
Produced by: AxCrypt Software Private Limited
Free Download: https://www.axcrypt.net/download
AxCrypt offers file security services to companies and organizations. By loading files to a cloud-based drive, you can share files with your team with its key sharing features. It's a folder-level encryption utility that you can apply to encrypt essential or big files on your computer. Let's go and learn how to use it.
How to Use:
Step 1. Launch AxCrypt and set a password for file or folder encryption on your PC.
Step 2. Select the encrypt mode - Recent Files or Secured Folders.
Step 3. Drag and drop target files or folders to the empty area in the software.
Then, your files and folders are encrypted.
Repeat the process to encrypt and secure all important files and folders on your computer.
#3. Encrypt PC Data with FolderLock - Paid
Supported OS: Windows OS, Android, and iOS
Produced by: NewSoftware
Free Download: https://www.newsoftwares.net/folderlock/
FolderLock is a Windows-based software produced by NewSoftware for file and folder-level encryption on Windows computers. Users can also apply it to backup the encrypted files, setting a password to lock an external storage drive like USB or external hard drive. Shredding files and permanently delete data from PC via this software is also nifty. Let's see how to use it on your Windows PC for file encryption.
How to Use:
Step 1. Launch Folder Lock and enter your Master password, click OK.
Step 2. Click Lock Folders > Add Items to Lock > Add Folders.
Step 3. Browse to select a folder that you need to lock, and click OK to confirm.
Now, your folder is locked and encrypted. You can neither open it nor access the saved files. To re-access these files, you need to right-click these files and select Unlock.
#4. Encrypt PC Drive with BitLocker - Free
Supported OS: Windows OS
Produced by: Microsoft
Free Download: Windows built-in tool, installation is not needed.
BitLocker is a reliable free disk encryption software that allows you to directly encrypt and password protect everything on your local disk and even external hard drive. Let's see how to use it and safely protect your computer now.
How to Use:
Step 1. Open This PC/My Computer, right-click the target drive, and select Turn on BitLocker.
Step 2. Check Use a password to unlock the drive, and add a password to encrypt your drive.
Step 3. Save and back up the encryption key, select Save to a file here. Then click Next.
Step 4. Check Encrypt entire drive (slower but best for PC and drives already in use) and click Next.
Step 5. Check Compatible mode (best for drives that can be moved from this device) and click Next.
Step 6. Click Start encryption and wait for the process to complete.
Once down, you'll see BitLocker displaying Encryption of *: is complete. It means the encryption process is done. If you tend to encrypt the entire computer, repeat the above steps to set a password to all existing hard drives.
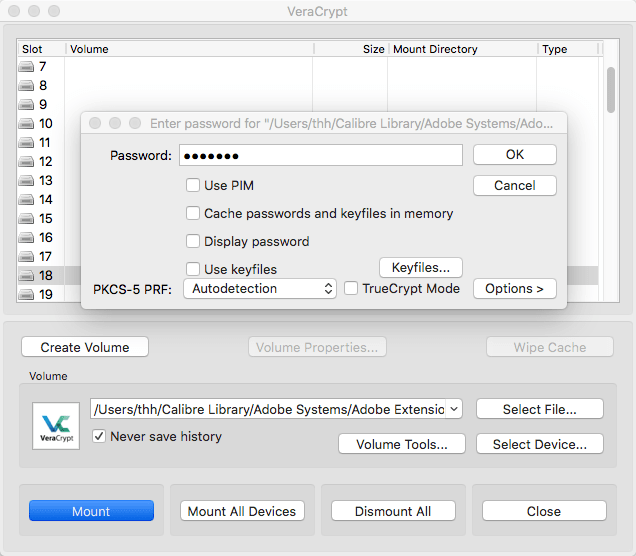
#5. Encrypt PC with VeraCypt - Open Source
Supported OS: Windows OS, macOS, and Linux
Produced by: IDRIX
Free Download: https://www.veracrypt.fr/en/Downloads.html
VeraCrypt is a free open-source disk encryption software for Windows, macOS, and Linux. It was developed by IDRX and based on TrueCrypt 7.1a. It provides you with enterprise-grade encryption for important data. How to use it to encrypt computer drives? Let's see the details.
How to Use:
Step 1. Click Create Volume.
Step 2. Check Encrypt a non-system partition/drive and click Next.
Step 3. Select Standard VeraCrypt volume and click Next.
Step 4. Click Select Device... to browse the drive that you need to encrypt and click OK. Then click Next to continue.
Free File Encryption Software For Mac
Step 5. Select Encrypt partition in place to avoid data overwritten error, then click Next.
Step 6. Select Encryption Algorithm and click Next.
Step 7. Set a password to encrypt the drive and click Next.
Step 8. Wait for the encryption process to complete, or click Next to jump this procedure.
Step 9. Select the Wipe mode as None (fastest) and click Next.
Step 10. Click Encrypt.
Wait patiently to let the software complete the encryption process on your computer. To secure more drives, repeat the above steps on your PC.
Encrypting Computer Drive, Files, Folders Is Important, Go and Secure Your Data Now
On this page, we collect 5 best PC encryption software that helps you to safely encrypt computer hard drive, external disk, files, and folders on both Windows and Mac computers.
Some of you may have the same question here: which tool is the best for PC encryption?
Here is EaseUS Editors Choices, and you can give it a try:
- For an instant, complete, and paid encryption software for Windows PC, EaseUS LockMyFile stands out. It's flexible for file locking, folder and drive locking, folder encryption, and file shredding.
- For free and easy PC encryption software, BitLocker deserves your trust.
- For a reliable Mac encryption software, give AxCrypt a shot.
Note that encrypting essential files and folders, or even a local drive on your computer is fairly important for securing data from unknown visitors, hackers, or malware on your PC. Go and follow to secure your data now.
-->Encryption and digital certificates are important considerations in any organization. By default, Exchange Server is configured to use Transport Layer Security (TLS) to encrypt communication between internal Exchange servers, and between Exchange services on the local server. But, Exchange administrators need to consider their encryption requirements for communication with internal and external clients (computers and mobile devices), and external messaging servers.
Jan 27, 2011 Can't sign in to Lync server using Mac Communicator 11. Message is: Either date and time settings are incorrect, or the digital certificate file is not valid or installed on your computer. If date and time are corect, see your network administrator to verify that your digital certificate file is valid and installed. 'Microsoft Communicator cannot sign you in. Either date and time settings are incorrect, or the digital certificate file is not valid or installed on your computer. If date and time are correct (they are), see your network administrator (I'm one) to verify that your digital certificate is valid and installed.'
Note
Exchange Server 2019 includes important changes to improve the security of client and server connections. The default configuration for encryption will enable TLS 1.2 only and disable support for older algorithms (namely, DES, 3DES, RC2, RC4 and MD5). It will also configure elliptic curve key exchange algorithms with priority over non-elliptic curve algorithms. In Exchange Server 2016 and later, all cryptography settings are inherited from the configuration specified in the operating system. For additional information, see Exchange Server TLS Guidance.
- May 23, 2007 Microsoft Messenger cannot sign you in. Either data and time settings are incorrect, or the digital certificate file is not valid or installed on your computer. If date and time are correct, see your network administrator to verify that the digital certificate file is valid and installed.
- Before you can establish a Partner Center account, you need to get a code signing certificate to secure your digital information. This certificate is the accepted standard for establishing your company’s ownership of the code you submit. It allows you to digitally sign PE binaries, such as.exe,.cab,.dll,.ocx,.msi,.xpi and.xap files.
- Microsoft proceeds with the classification for all of its products and technologies prior to their release to market. Customers and partners who proceed with the export of a Microsoft product may use the ECCN provided by Microsoft to complete the Automated Export System (AES) or other documentation required for the export operation.
This topic describes the different types of certificates that are available, the default configuration for certificates in Exchange, and recommendations for additional certificates that you'll need to use with Exchange.
For the procedures that are required for certificates in Exchange Server, see Certificate procedures in Exchange Server.
Digital certificates overview
Online Password Encryption
Digital certificates are electronic files that work like an online password to verify the identity of a user or a computer. They're used to create the encrypted channel that's used for client communications. A certificate is a digital statement that's issued by a certification authority (CA) that vouches for the identity of the certificate holder and enables the parties to communicate in a secure manner by using encryption.
Digital certificates provide the following services:
Encryption: They help protect the data that's exchanged from theft or tampering.
Authentication: They verify that their holders (people, web sites, and even network devices such as routers) are truly who or what they claim to be. Typically, the authentication is one-way, where the source verifies the identity of the target, but mutual TLS authentication is also possible.
Certificates can be issued for several uses. For example: web user authentication, web server authentication, Secure/Multipurpose Internet Mail Extensions (S/MIME), Internet Protocol security (IPsec), and code signing.
A certificate contains a public key and attaches that public key to the identity of a person, computer, or service that holds the corresponding private key. The public and private keys are used by the client and the server to encrypt data before it's transmitted. For Windows users, computers, and services, trust in the CA is established when the root certificate is defined in the trusted root certificate store, and the certificate contains a valid certification path. A certificate is considered valid if it hasn't been revoked (it isn't in the CA's certificate revocation list or CRL), or hasn't expired.
The three primary types of digital certificates are described in the following table.
| Type | Description | Advantages | Disadvantages |
|---|---|---|---|
| Self-signed certificate | The certificate is signed by the application that created it. | Cost (free). | The certificate isn't automatically trusted by client computers and mobile devices. The certificate needs to be manually added to the trusted root certificate store on all client computers and devices, but not all mobile devices allow changes to the trusted root certificate store. Not all services work with self-signed certificates. Difficult to establish an infrastructure for certificate lifecycle management. For example, self-signed certificates can't be revoked. |
| Certificate issued by an internal CA | The certificate is issued by a public key infrastructure (PKI) in your organization. An example is Active Directory Certificate Services (AD CS). For more information, see Active Directory Certificate Services Overview. | Allows organizations to issue their own certificates. Less expensive than certificates from a commercial CA. | Increased complexity to deploy and maintain the PKI. The certificate isn't automatically trusted by client computers and mobile devices. The certificate needs to be manually added to the trusted root certificate store on all client computers and devices, but not all mobile devices allow changes to the trusted root certificate store. |
| Certificate issued by a commercial CA | The certificate is purchased from a trusted commercial CA. | Simplified certificate deployment, because all clients, devices, and servers automatically trust the certificates. | Cost. You need to plan ahead to minimize the number of certificates that are required. |
To prove that a certificate holder is who they claim to be, the certificate must accurately identify the certificate holder to other clients, devices, or servers. The three basic methods to do this are described in the following table. Microsoft office for mac multiple users.
| Method | Description | Advantages | Disadvantages |
|---|---|---|---|
| Certificate subject match | The certificate's Subject field contains the common name (CN) of the host. For example, the certificate that's issued to www.contoso.com can be used for the web site https://www.contoso.com. | Compatible with all clients, devices, and services. Compartmentalization. Revoking the certificate for a host doesn't affect other hosts. | Number of certificates required. You can only use the certificate for the specified host. For example, you can't use the www.contoso.com certificate for ftp.contoso.com, even when the services are installed on the same server. Complexity. On a web server, each certificate requires its own IP address binding. |
| Certificate subject alternative name (SAN) match | In addition to the Subject field, the certificate's Subject Alternative Name field contains a list of multiple host names. For example: • www.contoso.com • ftp.contoso.com • ftp.eu.fabirkam.net | Convenience. You can use the same certificate for multiple hosts in multiple, separate domains. Most clients, devices, and services support SAN certificates. Auditing and security. You know exactly which hosts are capable of using the SAN certificate. | More planning required. You need to provide the list of hosts when you create the certificate. Lack of compartmentalization. You can't selectively revoke certificates for some of the specified hosts without affecting all of the hosts in the certificate. |
| Wildcard certificate match | The certificate's Subject field contains the common name as the wildcard character (*) plus a single domain or subdomain. For example, *.contoso.com or *.eu.contoso.com. The *.contoso.com wildcard certificate can be used for: • www.contoso.com • ftp.contoso.com • mail.contoso.com | Flexibility. You don't need to provide a list of hosts when you request the certificate, and you can use the certificate on any number of hosts that you may need in the future. | You can't use wildcard certificates with other top-level domains (TLDs). For example, you can't use the *.contoso.com wildcard certificate for *.contoso.net hosts. You can only use wildcard certificates for host names at the level of the wildcard. For example, you can't use the *.contoso.com certificate for www.eu.contoso.com. Or, you can't use the *.eu.contoso.com certificate for www.uk.eu.contoso.com. Older clients, devices, applications, or services might not support wildcard certificates. Wildcards aren't available with Extended Validation (EV) certificates. Careful auditing and control is required. If the wildcard certificate is compromised, it affects every host in the specified domain. |
Certificates in Exchange
When you install Exchange 2016 or Exchange 2019 on a server, two self-signed certificates are created and installed by Exchange. A third self-signed certificate is created and installed by Microsoft Windows for the Web Management service in Internet Information Services (IIS). These three certificates are visible in the Exchange admin center (EAC) and the Exchange Management Shell, and are described in the following table:
| Name | Comments |
|---|---|
| Microsoft Exchange | This Exchange self-signed certificate has the following capabilities: • The certificate is automatically trusted by all other Exchange servers in the organization. This includes any Edge Transport servers subscribed to the Exchange organization. • The certificate is automatically enabled for all Exchange services except Unified Messaging, and is used to encrypt internal communication between Exchange servers, Exchange services on the same computer, and client connections that are proxied from the Client Access services to the backend services on Mailbox servers. (Note: UM is not available on Exchange 2019.) • The certificate is automatically enabled for inbound connections from external SMTP messaging servers, and outbound connections to external SMTP messaging servers. This default configuration allows Exchange to provide opportunistic TLS on all inbound and outbound SMTP connections. Exchange attempts to encrypt the SMTP session with an external messaging server, but if the external server doesn't support TLS encryption, the session is unencrypted. • The certificate doesn't provide encrypted communication with internal or external clients. Clients and servers don't trust the Exchange self-signed certificate, because the certificate isn't defined in their trusted root certification stores. |
| Microsoft Exchange Server Auth Certificate | This Exchange self-signed certificate is used for server-to-server authentication and integration by using OAuth. For more information, see Plan Exchange Server integration with SharePoint and Skype for Business. |
| WMSVC | This Windows self-signed certificate is used by the Web Management service in IIS to enable remote management of the web server and its associated web sites and applications. If you remove this certificate, the Web Management service will fail to start if no valid certificate is selected. Having the service in this state can prevent you from installing Exchange updates, or uninstalling Exchange from the server. For instructions on how to correct this issue, see Event ID 1007 - IIS Web Management Service Authentication |
The properties of these self-signed certificates are described in the Properties of the default self-signed certificates section.
These are the key issues that you need to consider when it comes to certificates in Exchange:
You don't need to replace the Microsoft Exchange self-signed certificate to encrypt network traffic between Exchange servers and services in your organization.
You need additional certificates to encrypt connections to Exchange servers by internal and external clients.
You need additional certificates to force the encryption of SMTP connections between Exchange servers and external messaging servers.
The following elements of planning and deployment for Exchange Server are important drivers for your certificate requirements:
Load balancing: Do you plan to terminate the encrypted channel at load balancer or reverse proxy server, use Layer 4 or Layer 7 load balancers, and use session affinity or no session affinity? For more information, see Load Balancing in Exchange 2016.
Namespace planning: What versions of Exchange are present, are you using the bound or unbound namespace model, and are you using split-brain DNS (configuring different IP addresses for the same host based on internal vs. external access)? For more information, see Namespace Planning in Exchange 2016.
Client connectivity: What services will your clients use (web-based services, POP, IMAP, etc.) and what versions of Exchange are involved? For more information, see the following topics:
Microsoft Communicator Mac Digital Certificate File Free
Certificate requirements for Exchange services
The Exchange services that certificates can be assigned to are described in the following table.
| Service | Description |
|---|---|
| IIS (HTTP) | By default, the following services are offered under the default website in the Client Access (frontend) services on a Mailbox server, and are used by clients to connect to Exchange: • Autodiscover • Exchange ActiveSync • Exchange admin center • Exchange Web Services • Offline address book (OAB) distribution • Outlook Anywhere (RPC over HTTP) • Outlook MAPI over HTTP • Outlook on the web • Remote PowerShell* Because you can only associate a single certificate with a website, all the DNS names that clients use to connect to these services need to be included in the certificate. You can accomplish this by using a SAN certificate or a wildcard certificate. |
| POP or IMAP | The certificates that are used for POP or IMAP can be different from the certificate that's used for IIS. However, to simplify administration, we recommend that you also include the host names that are used for POP or IMAP in your IIS certificate, and use the same certificate for all of these services. |
| SMTP | SMTP connections from clients or messaging servers are accepted by one or more Receive connectors that are configured in the Front End Transport service on the Exchange server. For more information, see Receive connectors. To require TLS encryption for SMTP connections, you can use a separate certificate for each Receive connector. The certificate must include the DNS name that's used by the SMTP clients or servers to connect to the Receive connector. To simplify certificate management, consider including all DNS names for which you have to support TLS traffic in a single certificate. To require mutual TLS authentication, where the SMTP connections between the source and destination servers are both encrypted and authenticated, see Domain Security. |
| Unified Messaging (UM) | For more information, see Deploying Certificates for UM. Note: UM is not available in Exchange 2019. |
| Hybrid deployment with Microsoft Office 365 | For more information, see Certificate Requirements for Hybrid Deployments. |
| Secure/Multipurpose Internet Mail Extensions (S/MIME) | For more information, see S/MIME for message signing and encryption. |
* Kerberos authentication and Kerberos encryption are used for remote PowerShell access, from both the Exchange admin center and the Exchange Management Shell. Therefore, you don't need to configure your certificates for use with remote PowerShell, as long as you connect directly to an Exchange server (not to a load balanced namespace). To use remote PowerShell to connect to an Exchange server from a computer that isn't a member of the domain, or to connect from the Internet, you need to configure your certificates for use with remote PowerShell.
Microsoft Communicator Mac
Best practices for Exchange certificates
Although the configuration of your organization's digital certificates will vary based on its specific needs, information about best practices has been included to help you choose the digital certificate configuration that's right for you.
Use as few certificates as possible: Very likely, this means using SAN certificates or wildcard certificates. In terms of interoperability with Exchange, both are functionally equivalent. The decision on whether to use a SAN certificate vs a wildcard certificate is more about the key capabilities or limitations (real or perceived) for each type of certificate as described in the Digital certificates overview.
For example, if all of your common names will be in the same level of contoso.com, it doesn't matter if you use a SAN certificate or a wildcard certificate. But, if need to use the certificate for autodiscover.contoso.com, autodiscover.fabrikam.com, and autodiscover.northamerica.contoso.com, you need to use a SAN certificate.
Use certificates from a commercial CA for client and external server connections: Although you can configure most clients to trust any certificate or certificate issuer, it's much easier to use a certificate from a commercial CA for client connections to your Exchange servers. No configuration is required on the client to trust a certificate that's issued by a commercial CA. Many commercial CAs offer certificates that are configured specifically for Exchange. You can use the EAC or the Exchange Management Shell to generate certificate requests that work with most commercial CAs.
Choose the right commercial CA: Compare certificate prices and features between CAs. For example:
Verify that the CA is trusted by the clients (operating systems, browsers, and mobile devices) that connect to your Exchange servers.
Verify that the CA supports the kind of certificate that you need. For example, not all CAs support SAN certificates, the CA might limit the number of common names that you can use in a SAN certificate, or the CA may charge extra based on the number of common names in a SAN certificate.
See if the CA offers a grace period during which you can add additional common names to SAN certificates after they're issued without being charged.
Verify that the certificate's license allows you to use the certificate on the required number of servers. Some CAs only allow you to use the certificate on one server.
Use the Exchange certificate wizard: A common error when you create certificates is to forget one or more common names that are required for the services that you want to use. The certificate wizard in the Exchange admin center helps you include the correct list of common names in the certificate request. The wizard lets you specify the services that will use the certificate, and includes the common names that you need to have in the certificate for those services. Run the certificate wizard when you've deployed your initial set of Exchange 2016 or Exchange 2019 servers and determined which host names to use for the different services for your deployment.
Use as few host names as possible: Minimizing the number of host names in SAN certificates reduces the complexity that's involved in certificate management. Don't feel obligated to include the host names of individual Exchange servers in SAN certificates if the intended use for the certificate doesn't require it. Typically, you only need to include the DNS names that are presented to the internal clients, external clients, or external servers that use the certificate to connect to Exchange.
For a simple Exchange Server organization named Contoso, this is a hypothetical example of the minimum host names that would be required:
mail.contoso.com: This host name covers most connections to Exchange, including Outlook, Outlook on the web, OAB distribution, Exchange Web Services, Exchange admin center, and Exchange ActiveSync.
autodiscover.contoso.com: This specific host name is required by clients that support Autodiscover, including Outlook, Exchange ActiveSync, and Exchange Web Services clients. For more information, see Autodiscover service.
Properties of the default self-signed certificates
Some of the more interesting properties of the default self-signed certificates that are visible in the Exchange admin center and/or the Exchange Management Shell on an Exchange server are described in the following table.
| Microsoft Exchange | Microsoft Exchange Server Auth Certificate | WMSVC | |
|---|---|---|---|
| Subject | CN=<ServerName> (for example, CN=Mailbox01) | CN=Microsoft Exchange Server Auth Certificate | CN=WMSvc-<ServerName> (for example, CN=WMSvc-Mailbox01) |
| Subject Alternative Names (CertificateDomains) | • <ServerName> (for example, Mailbox01) • <ServerFQDN> (for example, Mailbox01.contoso.com) | none | WMSvc-<ServerName> (for example, WMSvc-Mailbox01) |
| Has private key (HasPrivateKey) | Yes (True) | Yes (True) | Yes (True) |
| PrivateKeyExportable* | False | True | True |
| EnhancedKeyUsageList* | Server Authentication (1.3.6.1.5.5.7.3.1) | Server Authentication (1.3.6.1.5.5.7.3.1) | Server Authentication (1.3.6.1.5.5.7.3.1) |
| IISServices* | IIS://<ServerName>/W3SVC/1, IIS://<ServerName>/W3SVC/2 (for example, IIS://Mailbox01/W3SVC/1, IIS://Mailbox01/W3SVC/2) | none | none |
| IsSelfSigned | True | True | True |
| Issuer | CN=<ServerName> (for example, CN=Mailbox01) | CN=Microsoft Exchange Server Auth Certificate | CN=WMSvc-<ServerName> (for example, CN=WMSvc-Mailbox01) |
| NotBefore | The date/time that Exchange was installed. | The date/time that Exchange was installed. | The date/time that the IIS Web Manager service was installed. |
| Expires on (NotAfter) | 5 years after NotBefore. | 5 years after NotBefore. | 10 years after NotBefore. |
| Public key size (PublicKeySize) | 2048 | 2048 | 2048 |
| RootCAType | Registry | None | Registry |
| Services | IMAP, POP, IIS, SMTP | SMTP | None |
*These properties aren't visible in the standard view in the Exchange Management Shell. To see them, you need to specify the property name (exact name or wildcard match) with the Format-Table or Format-List cmdlets. For example:
Get-ExchangeCertificate -Thumbprint <Thumbprint> Format-List *Get-ExchangeCertificate -Thumbprint <Thumbprint> Format-Table -Auto FriendlyName,*PrivateKey*
For more information, see Get-ExchangeCertificate.
Further details about the default self-signed certificates that are visible in Windows Certificate Manger are described in the following table.
Best Free File Encryption Software For Mac
| Microsoft Exchange | Microsoft Exchange Server Auth Certificate | WMSVC | |
|---|---|---|---|
| Signature algorithm | sha1RSA | sha1RSA | sha1RSA |
| Signature hash algorithm | sha1 | sha1 | sha1 |
| Key usage | Digital Signature, Key Encipherment (a0) | Digital Signature, Key Encipherment (a0) | Digital Signature, Key Encipherment (a0), Data Encipherment (b0 00 00 00) |
| Basic constraints | • Subject Type=End Entity• Path Length Constraint=None. | • Subject Type=End Entity• Path Length Constraint=None | n/a |
| Thumbprint algorithm | sha1 | sha1 | sha1 |
Free Folder Encryption
Typically, you don't use Windows Certificate Manger to manage Exchange certificates (use the Exchange admin center or the Exchange Management Shell). Note that the WMSVC certificate isn't an Exchange certificate.